Battery strap PTCs, or Positive Temperature Coefficient devices(a fancy way of saying its resistance increases with an increase in temperature), are components designed to protect batteries and associated circuits from overcurrent conditions. These are relatively unknown to folks outside the battery industry. Please don’t mistake them for the SMD fuses we fuse while designing PCBs for protection. Although they work on similar principles, the strap-ones are uniquely thin-shaped and attached directly to the batteries.
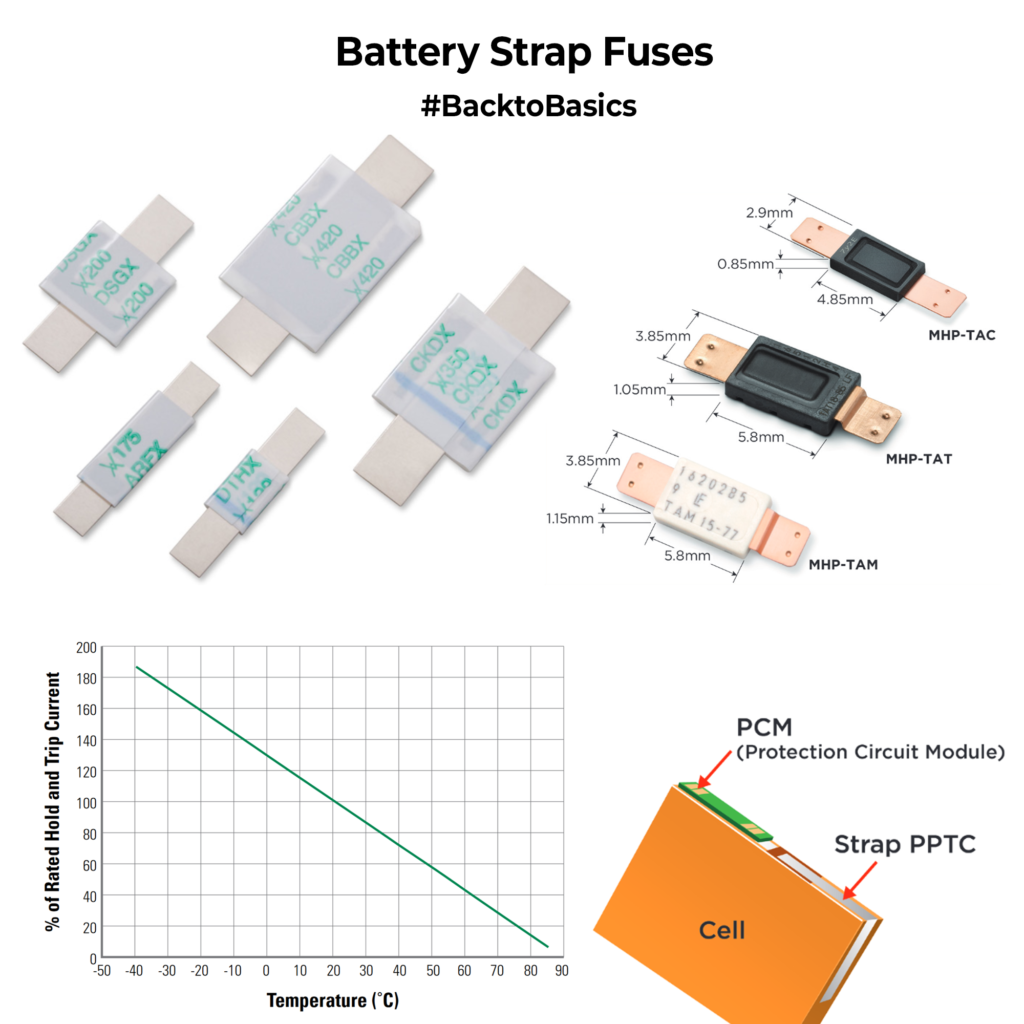
Battery strap PTCs act as self-resetting fuses. When an overcurrent condition occurs, the PTC heats up and its resistance rises dramatically, reducing the current flowing through it. This effectively limits the current to a safe level. Once the fault or overcurrent condition is removed, the PTC cools down, and its resistance decreases, allowing normal current flow to resume. Like all fuses, it will have a specific hold current(current allowed to pass in normal operation) and a trip current(current at which the device goes into high resistance mode). One major thing to keep in mind is that these hold/trip currents are temp-specific; as temperature increases, these values fall, and they will trip faster. In a way, it’s a nice thing because when the battery shorts, the temp shoots up and it reaches the trip point faster, but make sure it doesn’t trip in normal ambient or when the battery is getting charged(as the temp increases)
These fuses are usually spot welded or crimped on the battery terminals directly. It forms a great first line of protection in large battery packs and plays a crucial role in reliable and long-lasting battery solutions.
Have you ever used them in a project? How was your experience with it?